Install a Microsoft IIS5 or IIS6 certificate (or Exchange 2003+ for OWA service)
Warning : since March 2020, the TLS1.2 protocol is mandatory on web servers. Microsoft IIS5 and IIS6 are not compatible with this protocol. More information : TLS1.2 mandatory since March 2020
The procedure below is only valid if the CSR was generated via the IIS interface. If you have generated the private key and CSR via another means, you must follow this procedure:
- Private key and CSR generated via our Keybot tool: a PFX file (more infos) have to be generated and then be imported on the server. You will find a documentation on this link : Install a PFX file on your IIS 5 or 6
- Private key and CSR generated via a third party tool (OpenSSL for example): a PFX must be generated using OpenSSL for example (more infos). Then go back to the documentation to install a PFX file above.
1- Retrieve your certificate on your server
Download the overall file (.p7b) indicated in the delivery mail and save it on your desktop.Warning: If you are using a X509 certificate (.cer) you will have to install manually intermediate certificates and root certificate. It is way faster to follow this new installation procedure.
2- Import the certificate
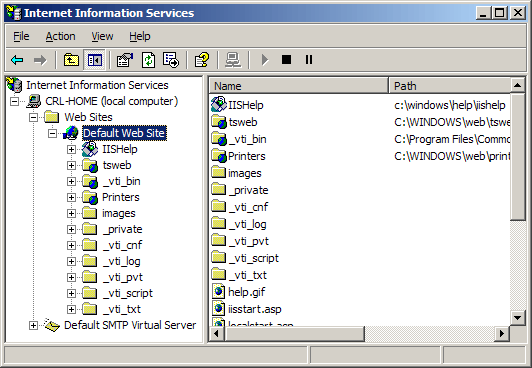
- Select "Administrative Tool" in the launch menu.
- Launch "Internet Services Manager" (IIS)"
- Go back on the website where you generated your certificate request (generaly the Default Web Site) and open the properties window. To do so, right click on the website or select Properties in the menu.
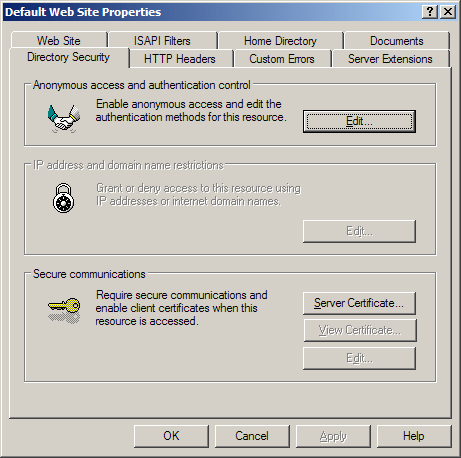
- Open the "Directory Security" tab.
- Click on "Server Certificate". The helper appears.
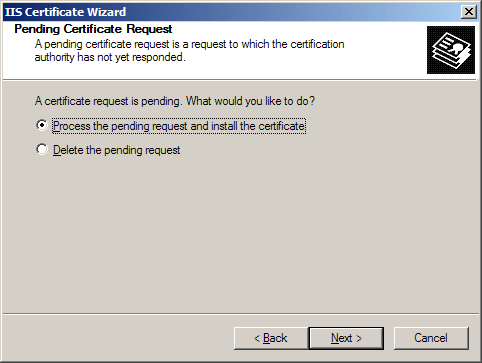
- Select the option: "Process the Pending Request and Install the Certificate". Then click Next.
- Place the filter on *.* and select the file inside which you downloaded your certificate. Click Next.
- Select the SSL port your website should be using (443 by défault) and click Next.
- Read the summary displayed on the screen and make sure you indicated the right certificate and click Next.
- You get a confirmation. Read it and click Finish. That's it!
3- Run a test
Do not forget to activate the encypherment (in the Directory security tab find the Secured communications section and click on Modify... Then tick Request a secured channel). If not non-SSL access will remain possible.Check the access of your website's secured pages with IE 6 and Firefox.
On your certificate status page, in your customer area at TBS CERTIFICATES, you will find a "Test the installation" button to test the correct installation of your of your certificate.

Particular case: renew a certificate
If you are renewing your certificate, you probably have created a temporary website not to interrupt the functioning of the main website. Renew a certificate with Microsoft IIS 5 or 6).In that case, follow the previous instructions to import the certificate on the temporary website.
Then activate the new certificate on the main site. To do so:
- Open the properties window of the main website. To do so, right click or select Properties in the menu.
- Open the "Directory Security" tab.
- Click on "Server certificate". The helper appears.
- Select the option "Replace the certificate" then click Next.
- In the dropdown menu select your new certificate (spot it with its expiration date). Click Next.
- Read the summary displayed on the screen and make sure you indicated the right certificate and click Next.
- Done! Your main site is now using the new certificate.
Enforce 128-bit
You can impose a 128-bit encryption level even with 40-bit guaranteed certificate. To do so, in the 'Security' tab of the repertory, next to 'Secured communication' click 'Modify' and tick '128-bit channel'.ADVICE AND RECOMMENDATIONS FROM TBS INTERNET
For security matters, it is advised to:
- disable SSLv2 and SSLv3. See Microsoft documentation: http://support.microsoft.com/kb/187498
- Disable RC4 and 3DES
- get protected from BEAST: consult the documentation
- get protected from unsecured renegociation: http://support.microsoft.com/kb/977377
- Enable safer ciphers, based on AES (256bits included)
And discover IIS Crypto by NARTAC, a tool with which you'll be able to easily make your IIS modifications (compatible IIS6)
Possible scenario
"SSL Handcheck error" or SSL does not start
Make sure our certificate and its private key have been correctly installed. To do so, launch the MMC of your Windows server. Your certificate may have been placed in "container user" instead of " local computer" (due to a window bug).You can troubleshoot with a local exportation and then a re-importation in the local computer.
http://support.microsoft.com/kb/939616/fr
Useful links
- Install a certificate after having deleted the pending certificate request
- Export your certificate and its private key on a Microsoft server (IIS5 / IIS6 / IIS7 / Exchange / ISA ...)
- Import a PFX file on your Microsoft server
- Install intermediate certificates or root certificates manually
- Enforce 128-bit under IIS
- Enable AES (256-bit included) on IIS6
- IIS mixes up websites and does not launch SSL after reboot
- Install a certificate after having delated the current certificate request
- Disable Thawte PCA (2036) root
- Disable COMODO RSA Certification Authority (2038) root
- Disable VeriSign Class 3 Public Primary Certification Authority root - G5 (2036)
- Configure a same certificate (wildcard, multiple-site) on a same port (443) in several site with IIS6
- Creating a directory starting with a dot on windows
- Install the new UserTrust intermediate certificate manually on Windows